Cybersecurity Policy and the Temple of Doom?
(… It’s not that hard to get started!)
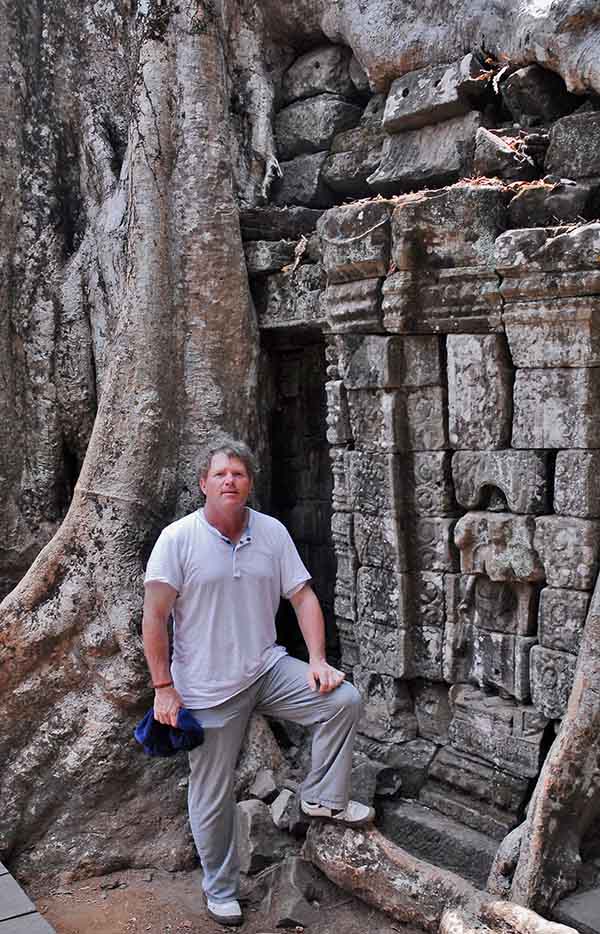
“They’re digging in the wrong place!”
Do you remember the first time you saw Raiders of the Lost Ark, how edge-of-the-seat everything seemed to be, and the sense of intrigue that held the storyline together? That now-legendary phrase, which a certain college professor-artifact hunter who, with his Egyptian sidekick, exclaimed when he and the good professor realized that the bad guys were looking for the fabled Ark of the Covenant in the wrong location, might have similarities with how organizations look at risk in today’s world of cyber espionage, phishing, and ransomware.
In the summer of 1981, the world was captivated by Dr. Henry Jones, and his friend, Sallah, through their journeys and as they discover the power of Divine Retribution that can come from gaining unauthorized access into something not meant for certain eyes.
Forty-one years later, and the legend of the Lost Ark, and the consequences that surrounded it, may remind businesses in all sectors, of the challenges they often face when trying to establish a company cybersecurity policy. The world has changed a lot since Indiana Jones led his would-be captors to the Well of Souls. And certainly, the Information Age has reshaped our world, our lives, how we evaluate “Risk” and even the way cybersecurity management and data security policies are defined.
Too often, companies will go through sort of an evolution of securing, shelving and discarding cyber security policies, guidelines—even products to manage them—moving from one “dig” to the next—all in an effort to achieve any combination of three things:
- Satisfy their shareholders.
- Address an audit requirement (usually SOC2).
- Solve a core set of problems associated with staying ahead of a new breed of “Bad Guys.”
Some critics might suggest the desire to make a few (billion) quick bucks might be leading many companies, to still be digging in the wrong place. Why? Because too often, we see process sacrificed on the altar of short-term attention, rather than fully planned, well-executed corporate cybersecurity policy development.
Let’s explore three fundamental reasons why cybersecurity initiatives fail, and maybe identify how to keep digging where we should be…
Cybersecurity policy procedures are hard to define.
They can be—but not impossible. The first order of business in addressing cybersecurity issues is by identifying what constitutes a “Risk” to your organization. This means going back to the basics and asking 10 fundamental questions relating to your business’ cybersecurity posture:
- What data does your organization consider to be an “Asset” to its success?
- Who else would consider that asset as valuable?
- Why is that data valuable?
- How do you access that asset (and for how long)?
- Who else has access to that asset (and why)?
- Where does that asset “live” (i.e., storage, cloud, on premises, somewhere else)?
- What happens to your business if those assets are not accessible?
- What processes do you have in place to address these concerns?
- Do you back up your systems and if so, how often?
- How often do you test your corporate cybersecurity policy?
Once you understand the scope of what is “at risk” in your business operations, you can begin addressing how to protect and defend against unwanted eyes, ears, and hands (virtually or otherwise). The Guidacent ThreatRecon Cybersecurity Services Team helps businesses of all sizes establish, mature and revise its policy for cybersecurity by addressing these 10 questions, which ultimately help simplify the process of securing the infrastructure and help establish an easy-to manage, easy-to-modify company cybersecurity posture.
Cybersecurity is constantly changing.
Like a flock of birds, risk management and corresponding efforts around cybersecurity tend to follow the least path of resistance, (and effort), which may lead to many different outcomes—none of which being those that will make the defining determination on whether you are actually securing your business environment or just spending money on another tool or failed process –either way—reminding you that you’re still digging in the wrong place.
While the process by which we build and manage a cybersecurity policy may be different depending on the asset, the environment, the size of the operation and the level of awareness within the organization, the process for establishing a consistent, repeatable, scalable and manageable framework can remain constant, especially if based on a national cybersecurity policy like the NIST Cybersecurity Framework.
Following a baseline and establishing a fundamental set of policies and procedures—even if only basic security guidelines around password integrity and access, can go a long way to reduce the risk of a compromise to your system.
Guidacent’s ThreatRecon Cybersecurity Services are designed to be tailored to any organization’s specific business operations. And taking a proactive approach to defending your system against cyberattacks by implementing proven processes means developing a consistent, dependable, scalable plan that will provide business owners and executives with the confidence that moving targets won’t matter—they’re still protected.
We don’t know where to start.
Your company’s cybersecurity policy will define the operating guidelines for how employees, executives, and third-party relationships consider computer security as part of their daily involvement with your business. Getting started on your policy is similar to planning a meeting: Identify what you need to address, how you want to address those issues and who needs to be involved, and then start putting the plan together.
Then it’s time to determine what you need and disregard that which you don’t. One good place to begin is by choosing to adopt a framework based on a national cybersecurity policy standard. The National Institute of Standards and Technology (NIST) framework is your best bet at building a foundation for cybersecurity. Should you need a more complex plan, look to the ISO 27001 or Center for Internet Security (CIS).
… Forty-one years. What we have learned since Dr Jones pulled that fabled box out of the pit of snakes is that there is no clear, complete solution to address the rising tide of criminal activity that target a business. But Guidacent can help your business establish those critical policies and procedures you need to help you keep focus on your business and its success.
And (with apologies to Dr Jones), if you find yourself falling down a hole with a bunch of asps (“very dangerous”), give Guidacent a call. We can help you dig in the right place!
Our Cybersecurity Services range from Cybersecurity Assessment Services, or if your business needs advisory services, we offer Cybersecurity Professional Services with consulting on-demand.